The OWASP Top 10 for Agentic Applications Gets a Lot Right. It Also Stops Where Real Control Has to Begin.
The new OWASP Top 10 for Agentic Applications 2026 is an important document. It is one of the better attempts I have seen to name the actual failure modes that show up once you move from static LLM use cases to autonomous, tool-using, multi-step systems. It correctly recognizes that agentic systems do not just answer questions. They plan, chain actions, invoke tools, persist context, communicate with other agents, and create operational effects across real systems. That shift matters because it changes AI risk from a content problem into an execution problem.
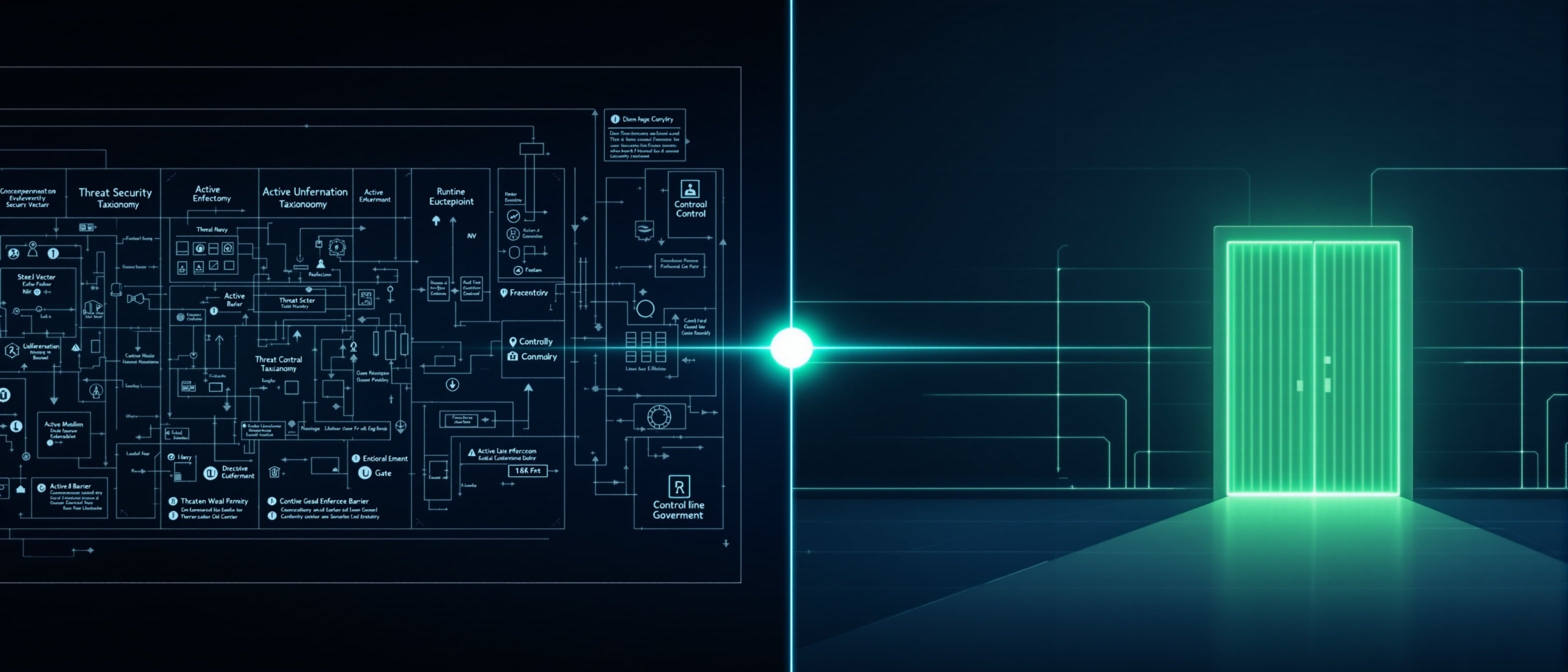
I want to give OWASP credit where it is due, explain where I think the document stops short, and then lay out a full crosswalk between the OWASP Top 10 for Agentic Applications and the Agentic Controls Reference (ACR) Standard. If your organization is using OWASP categories to frame risk, this crosswalk will show you where ACR provides the enforceable control structure that OWASP points toward but does not define.
OWASP tells you what can go wrong. ACR defines what must be true at runtime for the system to be governed.
What OWASP Gets Right
Before I get into the gaps, I want to be clear: the OWASP Top 10 for Agentic Applications is a meaningful contribution. There are several things it does well.
1. It names execution-layer risk, not just content-layer risk. This is a significant step forward. Previous frameworks treated AI risk almost entirely as a prompt-and-response problem. OWASP recognizes that agentic systems operate across tools, APIs, memory stores, and orchestration layers, and that risk lives at every one of those boundaries.
2. It treats agent identity and trust as first-class concerns. The inclusion of categories like Rogue Agents and Human-Agent Trust Exploitation reflects an understanding that agent behavior is not deterministic. Systems that plan their own execution paths and communicate with other agents require controls that go well beyond input filtering.
3. It calls out supply chain and dependency risks specific to agent architectures. The Agentic Supply Chain Vulnerabilities category is forward-looking and practical. Organizations building agentic systems are assembling components from multiple sources. OWASP is right to flag that the attack surface now includes tool registries, plugin ecosystems, and model providers.
4. It flags cascading failures as a category-level concern. Cascading Failures as a standalone category is an important signal. It tells the industry that agentic failure is not isolated. One compromised agent, one corrupted memory store, or one unchecked tool call can cascade across workflows. That framing is correct.
5. It gives the security community a shared vocabulary for agentic risk. Even where the categories are broad, the fact that OWASP has published a structured taxonomy for agentic risk gives security teams a common reference point for threat modeling, architecture review, and vendor assessment. That matters operationally.
Where OWASP Stops Short
With all of that said, the document has structural limitations that matter if you are trying to move from threat awareness to enforceable governance.
1. It identifies threats but does not define mandatory control conditions
OWASP names what can go wrong. It does not prescribe what must be true at runtime for a system to be considered governed. That distinction is critical. A threat taxonomy tells you where to look. A control standard tells you what has to hold.
2. It does not separate advisory risk from runtime enforcement
Many of the OWASP categories describe risks that can be mitigated through design guidance, policy documents, or deployment checklists. Those are useful, but they are not the same as runtime enforcement. There is no concept in the OWASP list of a control that fires at the moment of execution, a constraint that holds regardless of what the agent attempts.
3. It conflates agent-level risk with system-level architecture concerns
Some categories (like Excessive Agency or Insecure Inter-Agent Communication) describe risks at the individual agent level. Others (like Cascading Failures or Supply Chain Vulnerabilities) are system-level architecture concerns. Both are valid, but mixing them in the same flat list makes it harder to build control architectures that address each layer appropriately.
4. It does not define what "human oversight" means operationally
OWASP references human oversight repeatedly, but never defines what that looks like at runtime. Who has override authority? When must a human approve, review, or halt execution? What happens if the human is unavailable? Without those definitions, "human oversight" becomes an aspiration rather than a control.
5. It does not address the auditability problem
There is limited treatment of evidence, logging, and audit in the OWASP list. If an agent takes an action, OWASP does not define what evidence must be produced, how decisions must be logged, or what constitutes a sufficient audit trail. For regulated industries, that gap is significant.
6. It does not address observability as a control mechanism
Monitoring is mentioned in passing, but observability as a mandatory control mechanism is absent. There is no requirement for structured evidence of every decision, authority issuance, execution outcome, approvals, overrides, and containment actions end to end. ACR makes that explicit. It requires structured evidence, correlation across the action chain, retention, append-only handling for high-risk events, and exportable decision trails.
That is the difference between "we observed the incident" and "we can prove control was enforced."
7. It still leaves too much room for observational governance
This is the deepest issue.
The ACR Standard explicitly rejects policy-only governance, review-only governance, and observational mechanisms as sufficient for controlled systems. Control must happen before execution, at the input boundary, the execution boundary, and the output boundary. If the control plane is unavailable or indeterminate, the system must fail secure.
OWASP absolutely points toward runtime mitigations in many entries. But as a whole, it still reads like a very strong threat model plus mitigation catalog, not a standard that says: this system is controlled, this one is not.
That is the gap ACR is meant to close.
Where OWASP and ACR Align Well
The good news is there is a lot of overlap.
OWASP's instinct is often correct. ACR just turns those instincts into mandatory control conditions.
Here is the full crosswalk. Each entry maps one OWASP category to the corresponding ACR control pillars, identifies the relevant ACR sections, and includes my view on how the two relate. Click any row to expand the mapping detail.
ASI-01Excessive Agency→AuthorityIntentContainment
ACR addresses this directly through mandatory authority boundaries, pre-execution intent validation, and graduated containment. An agent operating under ACR cannot exceed its granted authority because the control plane enforces scope at every action boundary. OWASP names the risk. ACR defines the enforceable constraint.
ASI-02Misaligned Behaviors→IntentDrift DetectionObservability
Misalignment is fundamentally an intent validation failure. ACR requires that every agent action be evaluated against a declared intent contract before execution. Drift detection then monitors for behavioral deviation from that contract over time. OWASP flags the symptom. ACR enforces alignment as a runtime condition.
ASI-03Hallucinated Actions→IntentContainmentEvidence
Hallucinated actions occur when an agent executes tool calls or API requests based on fabricated parameters. ACR mitigates this through intent validation (does this action match the declared purpose?) and containment boundaries (is the action within permitted scope?). The evidence pillar then requires that all executed actions produce structured audit records so hallucinated actions can be identified and investigated.
ASI-04Agentic Supply Chain Vulnerabilities→AuthorityContainment
Supply chain risk is an authority and containment problem at its core. ACR requires that every external component, tool, and model provider be subject to the same authority constraints and containment boundaries as first-party components. Third-party tools do not get implicit trust. They operate within the same control plane enforcement as everything else.
ASI-05Unexpected Code Execution (RCE)→ContainmentAuthorityEvidence
RCE is the most acute containment failure. ACR requires that code execution capabilities be explicitly scoped, sandboxed, and subject to authority validation before invocation. Every execution event must produce evidence. If containment boundaries are breached, the system must fail secure and halt execution.
ASI-06Memory & Context Poisoning→EvidenceDrift DetectionContainment
Memory poisoning is particularly dangerous because it can alter agent behavior across sessions. ACR addresses this through evidence integrity requirements (append-only, tamper-evident logging), drift detection (identifying when behavior shifts due to corrupted context), and containment boundaries that limit the blast radius of poisoned memory stores.
ASI-07Insecure Inter-Agent Communication→AuthorityContainmentObservability
Multi-agent communication is an authority and containment problem. ACR requires that inter-agent messages be subject to the same authority validation and containment constraints as any other action. Agents cannot delegate authority they do not hold. Observability ensures that every inter-agent exchange is logged with full context for audit.
ASI-08Cascading Failures→Drift DetectionContainmentObservabilityHuman Authority
This is one of the strongest OWASP entries. ACR maps it to graduated containment, thresholded drift response, evidence lineage, and kill capability outside the agent runtime. The key ACR requirement here is that containment actions are not optional recommendations. They are mandatory state transitions that fire when drift thresholds are exceeded.
ASI-09Human-Agent Trust Exploitation→Human AuthorityIntentObservability
This is fundamentally a human authority problem. ACR defines exactly when human approval is required, what constitutes valid human override, and how the system must behave when human authority is absent. It is not enough to say "keep a human in the loop." ACR specifies the loop: when the human must act, what they must see, and what happens if they do not respond.
ASI-10Rogue Agents→AuthorityContainmentDrift DetectionEvidenceObservability
Rogue agents are the comprehensive failure case. Every ACR pillar is relevant because a truly rogue agent has escaped authority boundaries, violated intent contracts, breached containment, corrupted evidence, evaded drift detection, and operated outside observability. ACR treats this as the design case: the control architecture must prevent this state, and if it cannot, it must detect, contain, and halt it.
The Deeper Crosswalk: OWASP Categories Versus ACR's Six Pillars
If I were simplifying it for executives, I would say it this way:
OWASP tells you the ten ways agentic systems get into trouble. ACR tells you the six control capabilities a runtime system must have if you want those problems governed before consequence.
Here is how each ACR pillar maps back to the OWASP categories it addresses.
Human Authority
Defines who can authorize agent actions, when human approval is mandatory, what constitutes valid override, and how the system behaves when authority is absent or contested. This is the pillar OWASP references most often but never operationally defines.
Intent Validation
Requires that every agent action be evaluated against a declared intent contract before execution. If the action does not match the declared purpose, it is blocked. This is how ACR prevents misalignment and hallucinated actions at the execution boundary.
Containment
Enforces runtime boundaries on what an agent can access, invoke, and affect. Graduated containment means the system can tighten constraints dynamically based on risk signals. This is the most broadly applicable ACR pillar because most OWASP categories describe some form of boundary violation.
Evidence & Audit
Requires structured, tamper-evident records of every decision, action, authority issuance, and containment event. This is what makes the difference between "we think the agent did this" and "we can prove what happened and why."
Drift Detection
Monitors for behavioral deviation from declared baselines over time. Drift detection is what catches slow-burn failures: the agent that gradually shifts behavior, the memory store that accumulates poisoned context, the system that drifts outside its original operating envelope without triggering any single threshold.
Observability
Mandates end-to-end visibility into agent operations: decisions made, tools invoked, authority exercised, containment actions triggered, and outcomes produced. Observability is not monitoring. It is the structured, exportable evidence that the entire control architecture is functioning as designed.
The Bottom Line
The OWASP Top 10 for Agentic Applications is a strong threat taxonomy. It is not a control model. It tells you what can go wrong. It does not define the mandatory runtime conditions that make a system governed.
That is not a criticism of OWASP's intent. Threat taxonomies serve an important purpose. But if your organization is using OWASP categories as the basis for your agentic AI governance program, you need to pair them with an enforceable control standard. Otherwise, you have a risk register without a control plane.
The ACR Standard is built to close that gap. It takes the risks OWASP names and defines the runtime control conditions that must hold for the system to be governed. Every pillar is enforceable, auditable, and designed to operate at the execution boundary where agentic risk actually materializes.
If you are building, deploying, or governing agentic systems, I would encourage you to read both documents together. OWASP will sharpen your threat model. ACR will give you the control architecture to enforce it.
Want more governance insights?